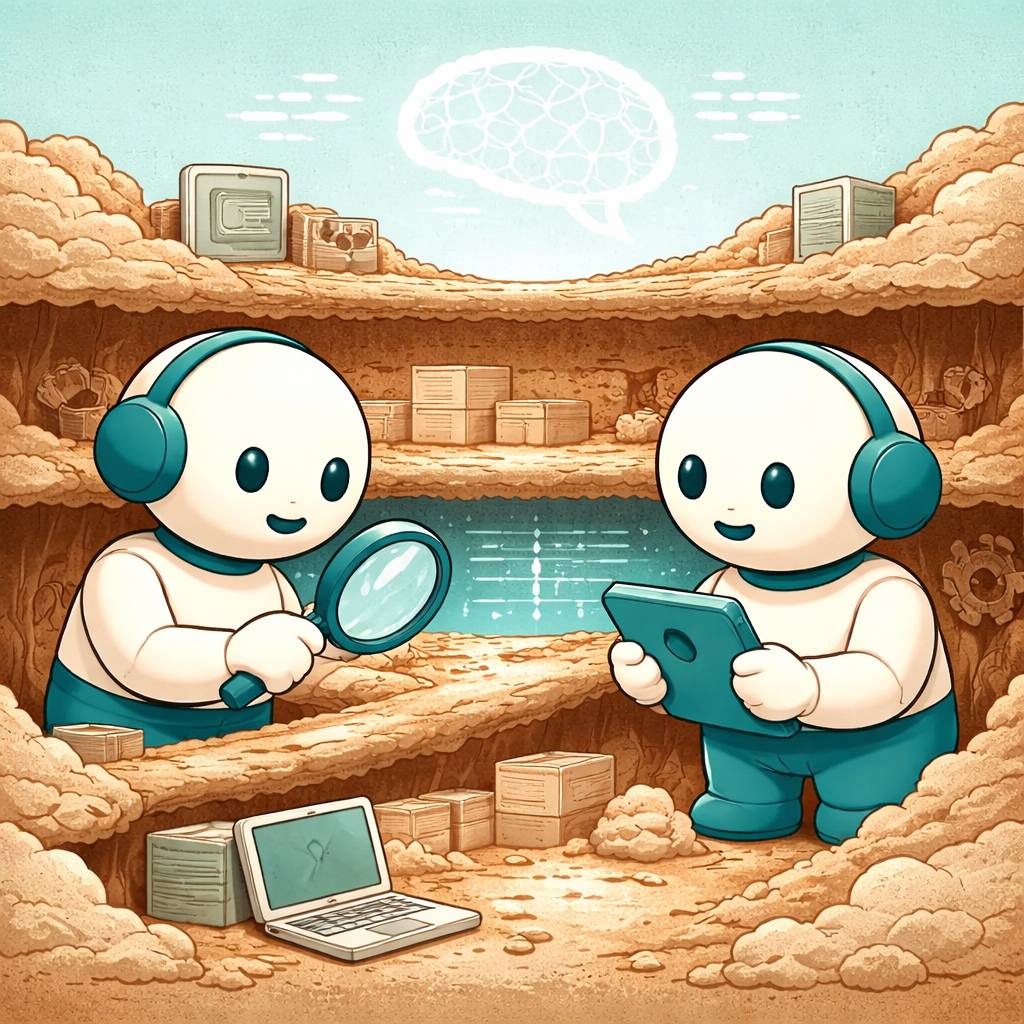
If legacy systems are the "Business Memory", the primary task of a modernization team is extraction. That memory isn't stored in a modern requirements document — it must be excavated from the layers of the existing operation.
Phase 1: Code Forensics (the "What")
Objective: Identify the "scars" in the logic that represent hidden business rules.
Flag "irrational" constants: Look for magic numbers in the code. A fixed multiplier like 1.042 is rarely a mistake — it's usually a specific tax or compliance calculation born from a historical crisis.
Trace the exceptions: Identify the IF/ELSE branches that handle edge cases. In legacy systems, those "edges" typically represent your most important clients or your most complex regulatory jurisdictions.
Phase 2: User Ethnography (the "How")
Objective: Discover the "Shadow System" that lives outside the software.
The Contextual Inquiry: Observe a power user without interrupting. Note every time they consult a sticky note, open a parallel Excel spreadsheet, or manually override a result.
The "Why" interview: When you identify a workaround, ask: "When did you start doing this?" This reveals Institutional Trauma — past failures that the current process was designed to prevent, even if the software shows no trace of them.
Phase 3: Data Archaeology (the "Output")
Objective: See what the system actually produces versus what it should produce.
Field misuse audit: Look for fields used in unintended ways (e.g., a "Notes" field storing "Contract Expiration Date"). This shows where the business has outgrown the original software schema.
Downstream dependency mapping: Trace where data goes after it leaves the system. The legacy may be doing "silent work" for teams (like Audit or Analytics) that aren't on the official stakeholder list.
Phase 4: The Memory Ledger (the Deliverable)
Before writing a single line of new code, categorize your findings into a Memory Ledger:
Modernization succeeds or fails before any new code exists. Teams that rebuild without extracting business memory don't modernize — they amputate. The Memory Ledger is the control point that separates continuity from rupture, making clear what must survive, evolve, or be discarded. Legacy systems are compressed history: decode them with rigor and the modernization preserves the business; ignore them and you erase it.
#digitaltransformation #LegacySystems #LegacyModernization #SoftwareArchitecture #BusinessContinuity
Ready to accelerate your business with innovative software solutions?
Get in touch to discover how our custom software solutions can digitally transform your business.
Let's talk?